






STOP THE SLOP
AI-generated images are flooding the internet. Verifiction catches the fakes before you share them—so you don’t spread the slop.



Our Technologies
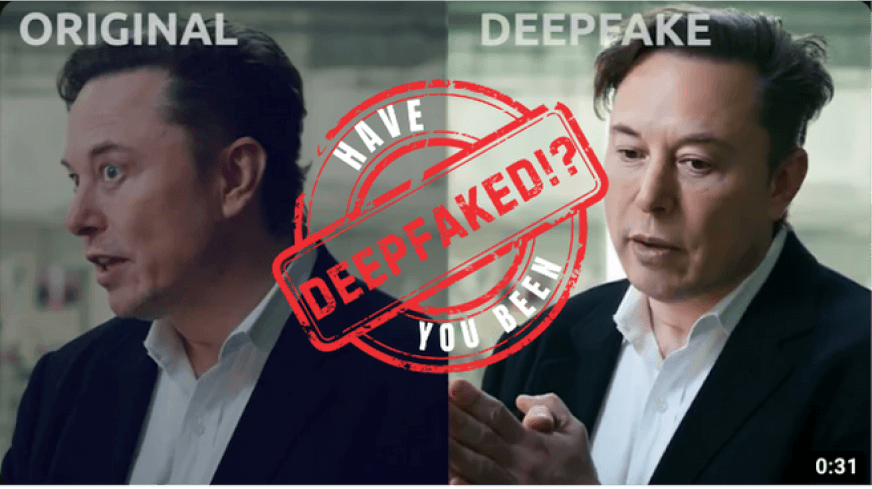
Deepfake Detector
Analyzes videos to discern real from fake, safeguarding against the spread of manipulated content.

Deepfake Authenticator
Combines protection against AI manipulation and defense against deepfake abuse, safeguarding content integrity and creators' rights comprehensively.

Deepfake Protector
Certifies video authenticity with watermarks, assuring viewers of unaltered content and creator's rights protection.
How Verifiction Can be Used

Protect digital and audio assets

Prevent images from being misused

Redact Images

Identify deepfakes

Autonomous Security Operations

Decentralized Identity Management

Resilient Infrastructure

Scalable Threat Intelligence
A Breakdown of Our Solutions

You have no idea how to take it down you Google for Solutions and it seems like a long arduous process No problem we got you.

You are not sure if the content you’re looking at is real or Fake. No problem, Verifiction’s detection system can determine whether the content you’re looking at is real or Fake.
Contact Details
© 2024 VERIFICTION ALL RIGHTS RESERVED
Privacy PolicyWe are C2PA compliant
© 2024 VERIFICTION ALL RIGHTS RESERVED
Privacy Policy





